Modifying Azure Active Directory B2C Password Policies using Powershell
Alfwyn Jordan, 31 July 2020
We’d previously set up a client with an Azure Active Directory B2C, and now we were receiving complaints about the clients’ passwords expiring.
To remedy this, we needed to change the password policy, and not just for one or two users but for all the users. The quickest method was to use the Azure Active Directory PowerShell for Graph module which can be found here. The link explains how to install this module using PowerShellGet.
This module allows you to perform a variety of actions on your Azure Active Directory from the PowerShell command line. For a full list of cmdlets available please check the Microsoft doc.
Once installed we need to enter our credentials. This is fairly straightforward. Run the following:
$Credential = Get-Credential
This opens a popup to enter your global administrator or user administrator account details.
Now to connect to your tenant, by running the following:
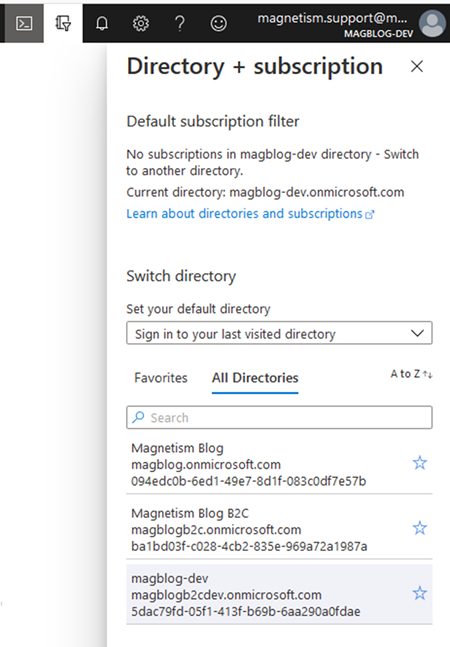
Connect-AzureAD -TenantId <<TenantId>> -Credential $Credential
The <<TenantId>
Now if you want to check the Password Policies of all your users, you’ll want to pipe it to a csv file so it’s actually workable, where <<Path>> is the path to your csv file you want to save the information to:
Get-AzureADUser | Select-Object -Property ObjectId, PasswordPolicies, SignInNames | Export-Csv -Path <<Path>>
Now, once you’re sure that this is the correct group of portal users, you can update the Password Policies, remembering that you may need to keep a previous policy, in our case Disable Strong Password, so simply add the new policy after the initial policies.
Get-AzureADUser -All $true| Set-AzureADUser -PasswordPolicies "DisableStrongPassword, DisablePasswordExpiration"
Depending on the number of users this could take a while, so grab a coffee, switch on Netflix and relax. Or maybe set it running before you head home.